Infrastructure Security in Cloud Computing
Introduction
Did you know cybercrime could cost the world $10.5 trillion by 2025? As more businesses adopt cloud solutions and rely on public cloud and private cloud computing environments, safeguarding cloud data is critical. Consequently, understanding infrastructure security in cloud computing and the role of Independent Software Providers is vital for protecting your assets.
Choosing the right cloud platform and cloud service provider ensures your data in the cloud is safe and compliant with security and compliance requirements. The goal of cloud infrastructure security; therefore, should be to implement rigorous security practices that protect cloud servers, cloud storage, and the entire ecosystem.
Let’s dive into the basics of infrastructure services and explore various security risks, from potential security threats in modern cloud environments to security protocols and security architecture that strengthen security in the cloud. By leveraging security offerings, such as AWS Security and IBM Cloud Pak for Security, businesses can build a comprehensive cloud infrastructure security framework to safeguard their computing environments.
Effective cloud infrastructure security operations are best when integrating code to cloud processes that allow organizations to develop and deploy infrastructure software using rigorous security practices. Solutions that enable robust security around data ensure businesses can strengthen their cloud infrastructure and meet today’s security challenges.
Understanding the Importance of Infrastructure Security in Cloud Computing
Businesses use the cloud to store and manage data, much like you might store valuable possessions in a safe or keep your money in a bank. Just as you rely on secure locks, alarm systems, or vaults to protect your property from theft, cloud environments require strong protection to safeguard sensitive information from cyber threats.
Strong infrastructure security services act as the virtual equivalent of these safeguards, forming the foundation that keeps your data safe. Just as a bank employs advanced security measures to protect your savings from being compromised, these services prevent unauthorized access, block security threats, and ensure that your critical information remains secure and intact. Without these protections, businesses leave their most valuable digital assets exposed to risks.
Key Components of Cloud Infrastructure Security
Just like the example above, a secure bank vault has multiple layers of protection, similarly cloud security relies on several key components to safeguard data and resources:
- Network Security
- Protects data as it moves across the cloud, similar to securing money during transport.
- Includes:
- Firewalls: Act as the locks on the vault, controlling what enters and exits.
- Intrusion Detection: Like security cameras, they monitor for suspicious activity.
- Secure VPNs: Provide encrypted “tunnels,” ensuring data remains safe during transit.
- Data Encryption
- Encrypts information in data centers to prevent unauthorized access, akin to securing valuables with a combination lock.
- Ensures that even if someone intercepts the data, they cannot read or use it.
- Access Controls and Identity Management
- Limits who can access cloud resources, reducing the risk of insider misuse, much like restricting access to a vault to authorized personnel only.
- Techniques include:
- Multi-factor Authentication (MFA)
- Role-based Access Controls (RBAC)
Common Security Threats in Cloud Environments
Understanding potential threats is as critical as knowing where a thief might strike. Here are common risks cloud environments face:
Threat |
Description |
Real-World Comparison |
|---|---|---|
| Data Breaches | Often result from cloud infrastructure weaknesses, exposing sensitive information to bad actors. | Like a break-in at a bank due to weak vault security. |
| DDoS Attacks | Overwhelm systems, causing downtime and financial losses. | Similar to a coordinated mob blocking access to a building, preventing normal operations. |
| Insider Threats | Occur when employees misuse their access to compromise data. | Equivalent to a bank employee giving away vault access or mismanaging sensitive client information. |
By recognizing these components and threats, businesses can proactively protect their cloud environments, just as individuals rely on secure measures to safeguard their most valuable possessions. Many businesses turn to Independent Software Providers for assistance in building a secure and protected infrastructure. These Providers provide specialized expertise, tools, and technologies—such as firewalls, encryption, and access controls—to fortify cloud systems against potential threats. Partnering with a trusted Provider ensures that businesses not only mitigate risks but also maintain compliance with security and regulatory requirements, enabling them to focus on growth with confidence.
Best Practices for Ensuring Cloud Infrastructure Security
Now that we understand the importance of securing cloud environments, let’s explore how to put that knowledge into action. Keeping your infrastructure safe starts with setting up strong security policies. These policies ensure that everyone involved knows their role in protecting valuable data and resources.
Being proactive in security management is essential. This means identifying, addressing, and preventing security threats before they can cause harm. Regular security audits also play a crucial role in this process, as they evaluate your system’s defenses, uncover vulnerabilities, and provide recommendations for improvement.
By staying proactive, you can stay one step ahead of potential threats. Incorporating security management into daily operations allows you to closely monitor risks. Additionally, collaborating with experts and learning from others in the field can further enhance your organization’s overall security posture.
- Regularly update and test your incident response plan.
- Ensure data encryption both in transit and at rest.
- Implement multi-factor authentication across your network.
- Conduct routine security audits to identify and rectify vulnerabilities.
- Establish clear and comprehensive security policies.
Following these security best practices makes your cloud infrastructure stronger. It helps keep your system safe from breaches and ensures a solid security management system for the long run.
Infrastructure Security in Cloud Computing Independent Software Providers
Independent Software Providers are key in cloud computing security because they provide the foundational tools and expertise needed to secure cloud environments effectively. They offer cloud security solutions to protect digital assets, ensuring that businesses can focus on their core operations without compromising on safety or performance. These Providers are critical for organizations that may not have the in-house resources to manage complex cloud security needs.
For example, Google Cloud uses advanced encryption and constant monitoring to protect your data. Microsoft Azure’s Security Center manages and protects your cloud environments. Amazon Web Services (AWS) has services like AWS Shield and AWS WAF to fight cyberattacks. Additionally, these Providers continuously update their offerings to stay ahead of evolving threats, giving businesses access to the latest in security technology and practices.
These Providers have many cloud security solutions for different businesses. Here’s a look at some key security features:
Provider |
Key Security Features |
|---|---|
| Google Cloud | Advanced encryption, continuous threat detection |
| Microsoft Azure | Integrated security management, threat protection |
| Amazon Web Services (AWS) | AWS Shield, AWS WAF |
Knowing how Providers secure cloud computing infrastructure helps you choose wisely. By partnering with a trusted Provider, you gain access to advanced tools and expert support that protect your digital assets. This allows your organization to focus on its core business model, rather than diverting resources to manage complex security challenges. The right cloud security solution not only keeps your data safe but also streamlines your operations, providing the peace of mind needed to drive innovation and growth without compromise.
Comparing Infrastructure Security Services Offered by Major Cloud Providers
When evaluating cloud services, it’s essential to understand the software and tools used to secure cloud environments. Providers like Google Cloud, Microsoft Azure, and AWS use advanced security solutions to keep your data and applications safe.
Google Cloud Security Measures
Google Cloud employs a suite of tools to ensure robust protection for your data and applications. Key software features include identity management systems, data encryption, and automated vulnerability scanning. These tools proactively detect threats and provide swift response capabilities, enabling continuous protection.
Microsoft Azure Security Center
The Microsoft Azure Security Center serves as a centralized platform for managing security across hybrid environments. It integrates seamlessly with Azure services, offering features like adaptive access controls and automated threat intelligence. These capabilities ensure compliance while providing resilience through real-time monitoring and response.
AWS Cloud Security Approach
AWS Cloud Security follows a shared responsibility model, supported by software-driven solutions like AWS Shield and AWS Macie. These tools automate security checks, enforce encryption, and manage identity access, enabling businesses to meet compliance standards while reducing manual effort.
Advanced Security Software for Cloud Infrastructure
Building on the foundational tools and services we just explored, it’s important to recognize that many cloud providers go beyond basic security measures. They offer advanced security software that provides deeper capabilities, focusing on proactive defense, continuous monitoring, and sophisticated risk mitigation. These enhanced solutions ensure that businesses are not only protected but are also equipped to adapt to evolving threats in a dynamic digital landscape.
Cloud Security Posture Management (CSPM)
CSPM tools actively monitor your cloud environment, detecting potential vulnerabilities and ensuring alignment with best practices. With automation at their core, these tools deliver real-time updates, enabling early issue resolution and streamlined compliance checks.
Security Monitoring and Response Software
Security monitoring and response platforms incorporate advanced intrusion detection, event logging, and automated alerts. These features empower businesses to respond rapidly to threats, minimizing damage and maintaining operational continuity.
Tool |
Primary Function |
Key Features |
|---|---|---|
| CSPM Solutions | Security Posture Management | Compliance automation, risk analysis, threat detection |
| SIEM Systems | Security Information and Event Management | Real-time alerts, incident response, data analysis |
| IAM Tools | Identity and Access Management | Role-based access control, multi-factor authentication, privilege management |
These software-driven solutions enhance cloud security, reduce operational risks, and help organizations adhere to compliance requirements. By leveraging these tools, businesses can safeguard their cloud environments while remaining agile in the face of emerging threats.
Integrating Security and Compliance in Cloud Computing Services
Effective cloud computing services rely on software solutions that integrate robust security measures with strict compliance protocols. Layers of protection—ranging from physical safeguards to advanced software tools—are essential to secure sensitive data and applications.
For industries like healthcare and finance, where regulatory compliance is non-negotiable, cloud providers offer specialized solutions tailored to meet stringent requirements. Features like real-time compliance reporting, automated risk assessments, and advanced access management ensure these needs are met efficiently.
By implementing a multilayered approach to security, businesses can maintain operational resilience and customer trust. Software-driven solutions that combine prevention, detection, and response capabilities not only secure data but also empower organizations to adapt to evolving risks and compliance demands.
How Independent Software Providers Use Vivantio to Support Cloud Computing
Independent Software Providers (ISPs) play a crucial role in delivering essential connectivity and foundational services that support cloud computing. To manage and optimize these services effectively, many ISPs utilize advanced service management platforms like Vivantio. These platforms enable ISPs to centralize support operations, streamline workflows, and enhance customer service delivery.
By leveraging Vivantio’s service management solutions, ISPs can efficiently handle service requests, monitor network performance, and promptly address issues, ensuring reliable and secure cloud services for their customers. This integration allows ISPs to focus on their core business objectives while maintaining high standards of service quality and customer satisfaction.
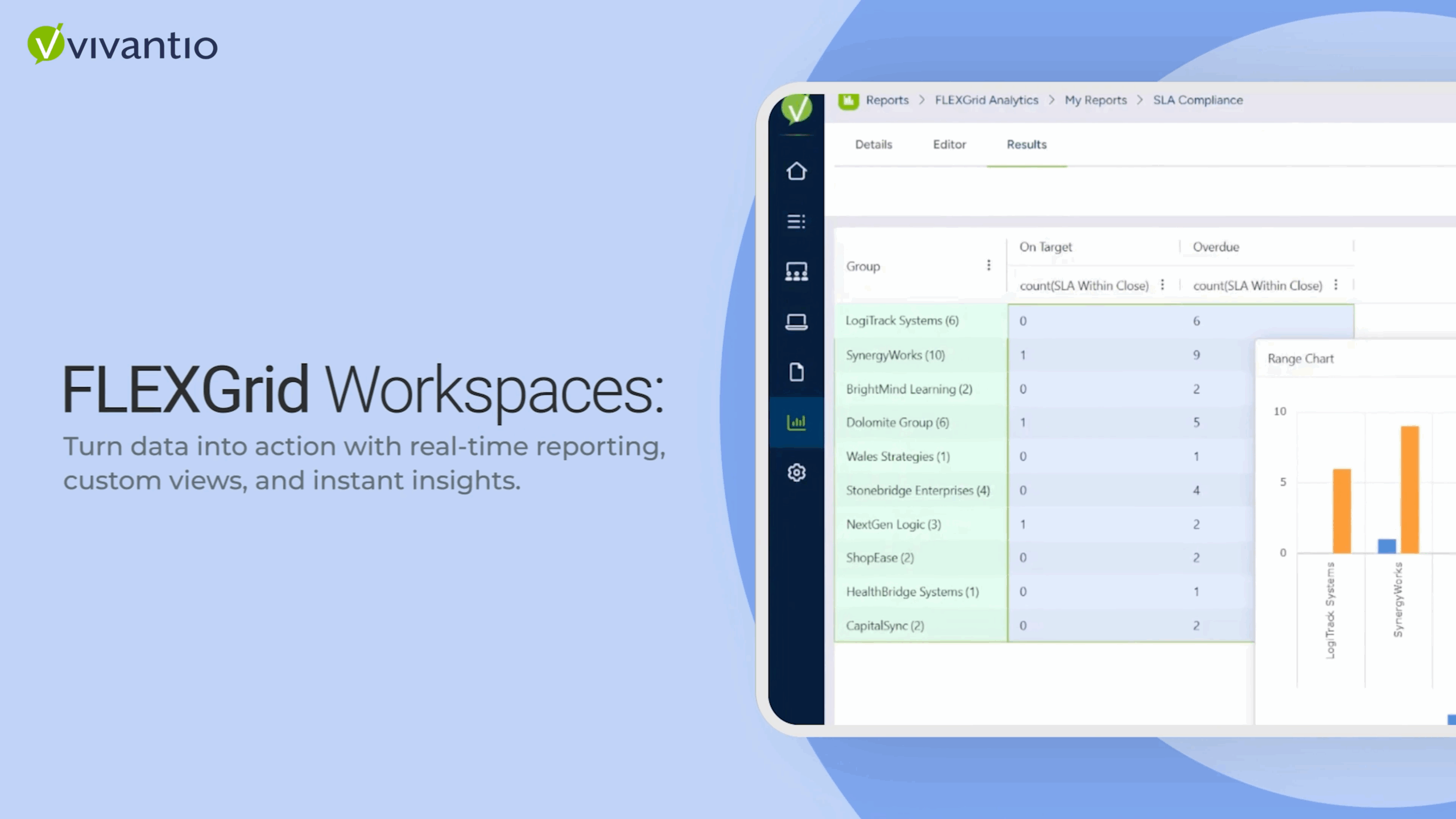
Key ways Vivantio supports ISPs include:
- Centralized Service Management: Consolidates customer interactions and service requests into a unified system, facilitating better coordination and faster response times.
- Workflow Automation: Automates routine tasks and processes, reducing manual effort and minimizing the risk of errors.
- Advanced Reporting and Analytics: Provides ITSM insights into service performance and customer satisfaction, enabling data-driven decision-making and continuous improvement.
With these capabilities, ISPs can enhance their operational efficiency, deliver superior cloud computing services, and strengthen their position in a competitive market.
Strengthen Your Cloud Security with Vivantio
Is your organization prepared to tackle the growing complexities of cloud security? With Vivantio’s advanced platform, you can enhance your cloud infrastructure’s protection and compliance with tools designed to safeguard your data and streamline security processes.
- Optimize Cloud Security Operations: Centralize monitoring and response to detect and mitigate threats efficiently.
- Enhance Threat Detection: Leverage real-time alerts and automated vulnerability assessments to stay ahead of potential risks.
- Ensure Compliance: Simplify audits and meet regulatory requirements with tools designed to track and report on your cloud security posture.
Take the next step toward fortifying your cloud environment:
- Schedule a Free Consultation: Explore how Vivantio can help secure your cloud infrastructure.
- Request a Demo: See Vivantio in action and discover how it can elevate your cloud security strategy.
Don’t wait to strengthen your defenses. Protect your business with the tools and expertise that ensure your cloud is safe, compliant, and ready for future challenges. Choose Vivantio to power your cloud security strategy today.